How does Dataslayer handle my data? Privacy and storage models explained
Wondering how your data is managed when using Dataslayer? Don't worry, in this article you will find everything you need to know about our privacy model and the different storage options available.
At Dataslayer, we take data privacy seriously. Whether you are handling sensitive campaign data for a large enterprise or managing reports for a small agency, you have options. Depending on your compliance requirements, performance needs, and internal policies, you can choose the model that best fits your organization.
Regardless of the model you choose, all data processed by Dataslayer is handled in compliance with ISO 27001 and ISO 27701 security standards. The models below determine where your data is stored and who controls it, not whether it is secure.
Before diving into the models, let's clarify two key concepts:
Connector: the data source Dataslayer connects to in order to extract your data (Google Ads, Meta Ads, TikTok Ads, etc.).
Destination: the place where your data is sent and stored (BigQuery, Google Sheets, Microsoft Excel, Power BI, etc.).
Dataslayer offers three data handling models. Here is a quick overview before we go into the details:
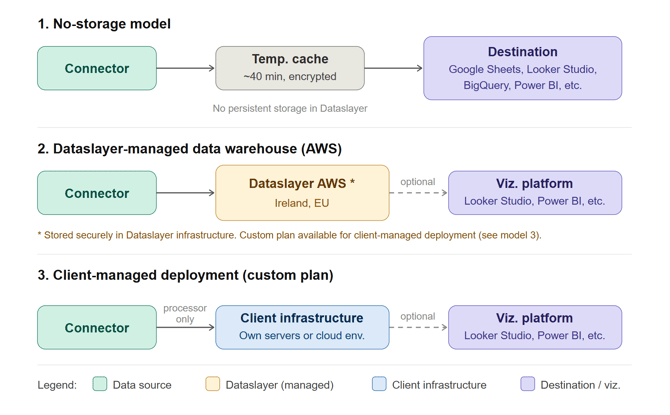
| No-storage model | Dataslayer-managed warehouse | Client-managed deployment | |
| Data stored in Dataslayer infrastructure | No (temp. cache only) | Yes (AWS, Ireland) | No (client infrastructure) |
| Client controls storage | Via destination | No, but data can be deleted at any time | Yes, full control |
| Dataslayer security scope |
Transit and temp. cache | Transit and storage | Transit and storage (on client infrastructure) |
| Best for | Maximum privacy | Balanced performance and compliance | Strict regulatory requirements |
1. No-storage model (maximum privacy)
With this model, your data flows directly from the connector to your chosen destination, without being stored anywhere in Dataslayer's infrastructure.
Here is how it works: your data is extracted from the source API, temporarily processed for consolidation, and sent straight to your destination (Google Sheets, Looker Studio, BigQuery, Power BI, etc.). The only exception is a short-lived encrypted cache (approximately 40 minutes) used to optimize performance, after which no data remains on our side.
Best for: users and organizations that want maximum privacy and full control over where their data lives.
2. Dataslayer-managed Data Warehouse (AWS)
With this model, your data is stored securely in Dataslayer's own infrastructure on Amazon Web Services, located in Ireland (EU). Your data is protected through encryption both in transit and at rest, and our infrastructure complies with ISO 27001 and ISO 27701 security standards.
Once your data is in the Dataslayer warehouse, you can optionally connect it to a visualization platform of your choice (Looker Studio, Power BI, etc.) to build your dashboards and reports. You retain the ability to delete your data at any time directly from the platform, without needing to contact us.
Best for: clients looking for a balance between performance, scalability, and compliance, without the overhead of managing their own infrastructure.
3. Client-managed Data Warehouse
This model is an extension of model 2. Instead of storing data in Dataslayer's AWS infrastructure, Dataslayer is deployed directly on the client's own servers or cloud environment. While the infrastructure belongs to the client, Dataslayer remains responsible for how data is written, encrypted, and managed during the process. Your team retains full control over storage, access, and data retention policies.
As with model 2, you can optionally connect your data to a visualization platform once it is in your infrastructure.
This option requires a custom plan. If you are interested, please reach out to our team to discuss your specific requirements.
Best for: enterprises and organizations with strict regulatory, legal, or internal compliance requirements.
A note on security layers
Security in Dataslayer works in independent but complementary layers:
-
The connector (origin) operates under the API-level security of the data source, Dataslayer only connects to verified, secure connectors.
-
Dataslayer's own layer is covered by ISO 27001 and ISO 27701 certifications, with encryption in transit and at rest across all models. In model 3, this responsibility extends to how data is stored on the client's infrastructure.
-
The destination layer depends on the platform or infrastructure the client chooses and operates under its own security policies.
Each layer is independent, and Dataslayer is accountable for its scope in every model.
Is using a Data Warehouse mandatory?
No. The data warehouse is completely optional. You can freely choose any other destination such as Google Sheets, Microsoft Excel, BigQuery, or any other supported destination. Keep in mind that your final level of data privacy will depend on the destination you select and its own data policies.
As always, if you have any questions about which model is right for you, don't hesitate to reach out via live chat on our website or via email. We are happy to help!